Cybercrime is a very lucrative and constantly expanding business. Each year there is an increase in the number of attacks targeting companies, according to CCN-CERT statistics, ransomware attacks increased dramatically in 2020, maintaining an upward trend to date. For that reason, cybersecurity and ethical hacking are becoming increasingly important in companies.
In addition, for some time now these attacks have become more complex, leaving behind the traditional method of only encrypting data. Now, attackers are not only looking to impact the organization’s operations, but are also seeking financial gain from these types of attacks by requesting a direct payment or extorting companies to avoid publishing stolen information on the Internet.
In 2020, the Maze group published on the Internet information stolen from HMR, a pharmaceutical company dedicated to health care research and development, after refusing to pay the ransom after an attack. Among the published data was personal information of employees; such as name, date of birth, health questionnaires and even results of HIV or drug tests. It is not necessary to mention the sensitivity of this personal data and the consequences of not protecting it correctly by failing to comply with legislations as important as GDPR, LOPD and others depending on the country where we are.
It is also quite common for these attacks to aim to harm the operations of an organization. In 2021, the criminal group REvil, well known for its ransomware attacks, attacked an Apple service provider, apparently managing to steal confidential information plans about future devices of the brand.
As proof of life, REvil published a total of 15 images of MacBook 2021 plans on its blog on the Dark Web and urging Apple to pay before May 1, 2021. Otherwise, they would publish information that they had previously stolen little by little on a daily basis.
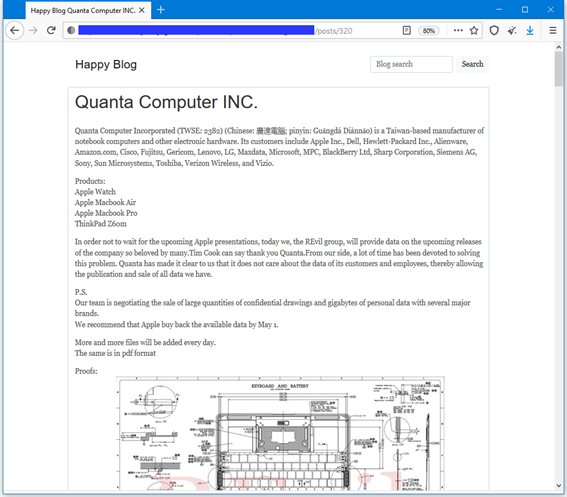
The American government launched actions to stop this type of actions of the different active criminal groups. One of the first results was the arrest of the REvil group, the most active and dangerous ransonware gang.
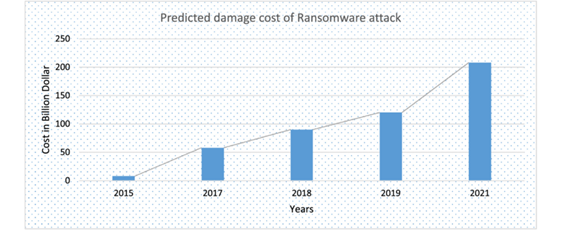
Due to the consequences of this type of attacks, organizations have put more and more resources into trying to avoid them. However, these types of attacks are very lucrative and those behind them are criminal organizations with a large amount of resources. From Cybercrime Magazine, they estimate that in 2025 the cost of cybercrime will cost $10.5 trillion.
The Professionalization of Crime
This professionalization of the industry has brought with it a series of associated services, such as what we know as RaaS, acronym for Ransomware as a Service.
In the RaaS model we have two main actors, the ransomware operator and the affiliates. The function of the operator is to develop the malware and prepare all the infrastructure behind it. On the other hand, the affiliates are responsible for gaining access, stealing the data and executing the ransomware on the network of an organization.
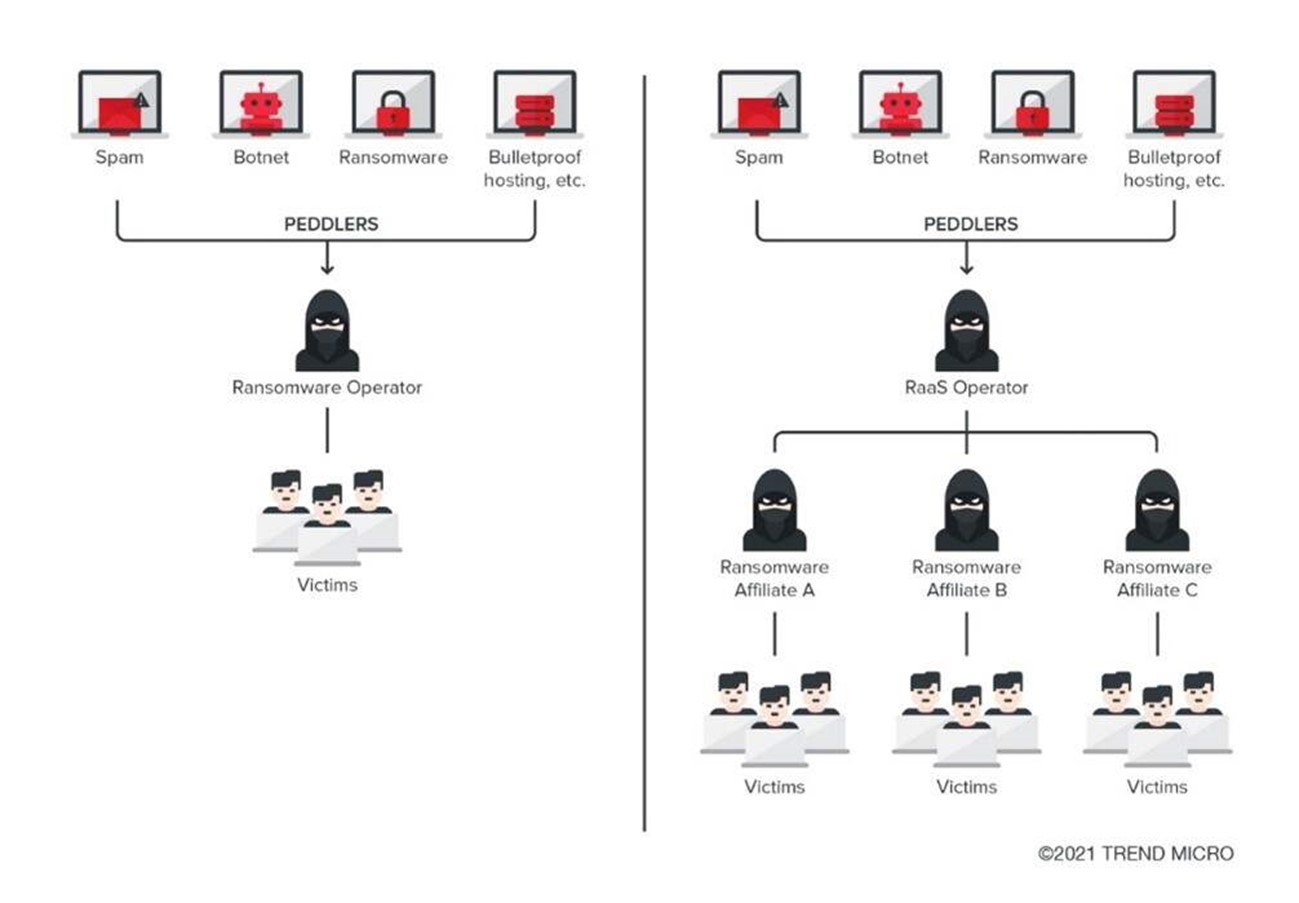
The REvil group offered its ransomware as a service, in exchange it asked for approximately 40% of the profits that the affiliates make thanks to its ransomware. These profits can be very high, since according to members of the group they managed to earn 100 million dollars in 2020.
According to Forbes estimates, in 2021 the cost of ransomware attacks amounted to 20 billion dollars, and they estimate that the number of victims who pay has risen to 58%. This causes the responsible groups to have more and more money and be able to carry out more sophisticated attacks.
How Does Ransomware Work?
Throughout this article we have talked a lot about ransomware, but how does a ransomware operate within our network? What do we see when we have received an attack of this type?
Ransomware is a type of malware that is responsible for encrypting and, in some cases, stealing files of great importance to an organization. These are attacks that, at their peak, can be targeted. That is, there is a previous stage of monitoring the organization, identifying what information is critical to it, the periods in which it can cause more damage, etc.
Normally there is a series of common stages within this type of attacks:
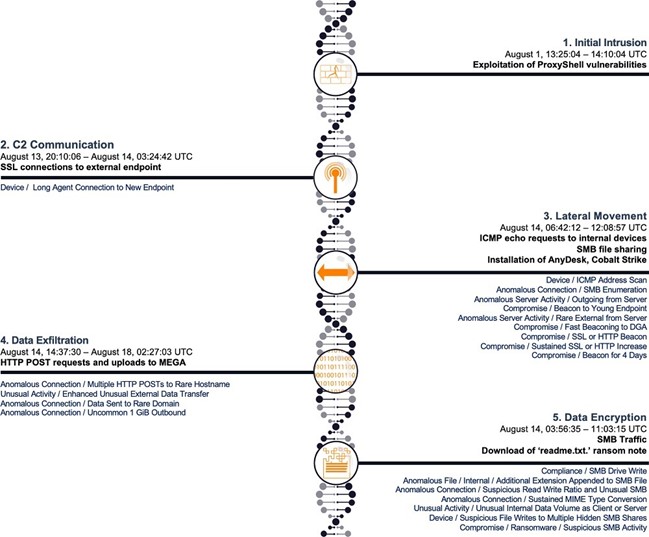
As we can see, a ransomware attack is composed of several phases. The first being to obtain initial access to the victim’s machine or network. This can be done in many ways, for example, by exploiting a vulnerability in an exposed service, or through a phishing e-mail, and even hiring an employee to provide us with some backdoor or information that facilitates the attack.
Once the attackers have gained access to the computer, their next objective will be to spread through the network to gain access to as many devices as possible (mail servers, file servers, shared folders, etc.).
To achieve this lateral movement between the systems of the organization, they sometimes resort to the exploitation of some vulnerability that is present in the system. In 2017, with the famous WannaCry ransomware, they took advantage of the vulnerability known as EternalBlue. This vulnerability took advantage of a failure in the SMB protocol, which is used to share files over the network and allowed code to be executed on the affected machines if an attacker exploited it properly.
Once they manage to compromise all or a large part of the equipment of an organization, the last phase of the attack, the encryption, begins. The ransomware will access all available storage media, and will look for what type of files are stored, in general it will focus on encrypting the office files, multimedia files, the source code of applications that are being developed and the information in the databases, in addition to the backup copies found.
Ransomware attacks are not always immediate, sometimes all phases of the attack are completed in less than 5 hours from the initial access, and in others they can remain hidden in our network for months.
This is because the attacks are usually quite sophisticated and seek to do as much damage as possible, so if there is nothing of value they can wait patiently. It is also likely that they will wait for the moment in which they can cause us the greatest possible economic losses, for example at the end of the year, or quarter closings.
To protect ourselves from this type of attacks it is not enough to make backup copies, since it is likely that the malware will spread to the network storage devices and backup copies. We must make backup copies periodically, verify the integrity of these and store them safely (outside the scope of the production network).
In addition, there are some more controls that have become important over time, because they are a very effective weapon against the behavior of a ransomware, such as ensuring the immutability of copies. That is, that no user or software has the possibility to change the status of a backup copy, neither encrypt it nor delete it. There are several providers and technologies that offer this type of measures, such as Amazon S3 with object locking.
As we have seen, there are many vectors that criminal organizations use to carry out their attacks and the wide diversity of techniques, tactics and procedures makes it very difficult to protect the applications that an organization uses in its day to day and that in most cases are the door that cybercriminals use to carry out this type of attacks.
That is why organizations must have implemented vulnerability management processes, based on automated tools and with a meticulous work that allows to explore in detail the different paths that an attacker could take to compromise the security of information.
What is Ethical Hacking?
Cybersecurity and ethical hacking are closely related, as both focus on protecting computer systems and networks against potential threats and attacks. However, ethical hacking is a practice that involves the use of hacking skills and techniques for the purpose of identifying and solving security vulnerabilities in computer systems and networks. Ethical hackers work in an authorized and legal manner to help companies and organizations improve the security of their systems, identifying and correcting vulnerabilities before they are exploited by similar groups of cybercriminals that we have mentioned previously.
Likewise, the main objective of ethical hacking is to protect the systems and confidential data of companies and organizations, ensuring that they are protected against malware attacks. To do this, the professionals in charge of ethical hacking perform penetration tests and vulnerability analysis, and then inform the organization about the problems found, and most importantly, they propose what to do to solve them before the production of a tool or a service, among others.
The complexity of this type of test is significant, so there are different ways to perform them, according to the purpose of these, although always with an agreement to avoid that this type of tests impact on the operation of information systems. In addition, it is essential to point out that these vulnerability analyzes within ethical hacking are carried out with the permission and authorization of the system owner, and are governed by strict codes of ethical conduct.
To know our vulnerabilities and how exposed we are to an attacker is one of the best exercises that a company can carry out, so it is of vital importance to periodically perform this type of tests in our corporate infrastructure and information systems. For that reason, to unite cybersecurity and ethical hacking, it is important that companies and organizations adopt a proactive security culture and see ethical hacking as an integral part of their security efforts.
What Position should Companies Take?
At the beginning of this article we mentioned that threats are constantly evolving, companies must also be.
Provide Training to your Employees.
We must be aware that to protect ourselves from a cyberattack we must not only focus on keeping our devices secure. Employee training is a fundamental pillar especially in security.
There are several tools that allow to carry out mailing and training campaigns that simulate attempts of Phising attacks to see the behavior of employees and reinforce the weak points that can be identified.
Related article: The importance of awareness and training in cybersecurity
Generate an Inventory of Assets and Classify Them
When it comes to keeping our organization secure, it is very important that we know what assets we are using, what is their purpose and what technologies each one uses. In addition, we should indicate which assets are critical and which store confidential or personal information.
If we do not know our assets it is very likely that our security policies are not adequate. One of the pillars of cybersecurity is to understand the business, because without this the controls that we implement will not be optimal.
Use Secure Configurations
To reduce the risk of suffering a cyberattack we should be aware that many of these take advantage of a bad configuration of assets and services.
We should fortify all equipment and services, especially those critical assets or exposed to the Internet, according to the CIS guides.
Implement and Audit Security Standards
The governance layer is very important. We have to be aware of what are the risks we face, which are more likely to materialize, which are the ones that would have the most impact and carefully choose our controls to deal with them. Above all, in large organizations it can be a challenge and that is why there are several standards that will allow to focus on what is important. Among these standards are the following:
- ISO 27001: It is an international standard for information security. It specifies the requirements necessary to establish, implement, maintain and improve an information security management system.
- ISO 27018: Provides a series of controls for the protection of personally identifiable information (PII) in the cloud for organizations that act as processors of this information.
- PCI-DSS: It is the data security standard used in the payment card industry. It is applicable to all entities that store, process or transmit cardholder data or sensitive authentication data.
- ENS: Recently modified, it is a law framed in the Spanish legislation, which proposes a series of measures to preserve the necessary conditions of trust in the use of electronic means to guarantee the security of systems, data, communications and electronic services.
This type of standards bring with them a periodic review, both internally and by a third party, which will allow us to identify weak points and continuously improve our security.
Pentesting
In addition to conducting audits on security standards, it is necessary that we undergo pentesting tests to detect design errors, or vulnerabilities that are present in our applications or services.
If we perform them periodically we can correct those problems that may pose a risk to our organization before we are victims of a real attack. However, we should also pay attention to cybersecurity news to help us detect new vulnerabilities discovered, and correct them before they are exploited by a malicious actor.
We recommend this article where we already reviewed in depth how companies can improve their cybersecurity strategies.
Conclusions
The traditional model of ransomware, in which only the data of companies was encrypted was able to cause a great disruption and damage to companies. As a result of the wide benefits that the groups dedicated to these operations have achieved, their attacks have become much more sophisticated and dangerous.
Even if we have a good backup policy, and we manage to keep them safe, we face a much greater risk, that of data breach. This can mean millionaire losses for companies, putting at risk both the personal data of workers and customers, as well as the intellectual property of the company.
Below we can see some recommendations:
- In most cases, employees are the first gateway for this type of attacks. Keep them trained and aware of the matter.
- Identify which are your critical information assets. Be consistent with this classification and put controls on the most critical information.
- Use secure configurations for services through CIS, STIG guides, etc. Especially those that are available externally.
- Security at the management level. Having a security strategy, identifying your risks and being consistent with them is essential to be protected against this type of attacks.
- Have a plan B. Continuity plans and DRPs that take into account this casuistry collected among their disaster scenarios.
- Monitoring of anomalous behavior, both on the network and on devices. How would you find out in your organization that your most important assets are being encrypted?
- More cybersecurity and ethical hacking audits carried out by professionals with vulnerability analysis.
- Pentesting of developed applications. These types of security reviews will close a gateway to vulnerabilities that are complex to detect.



