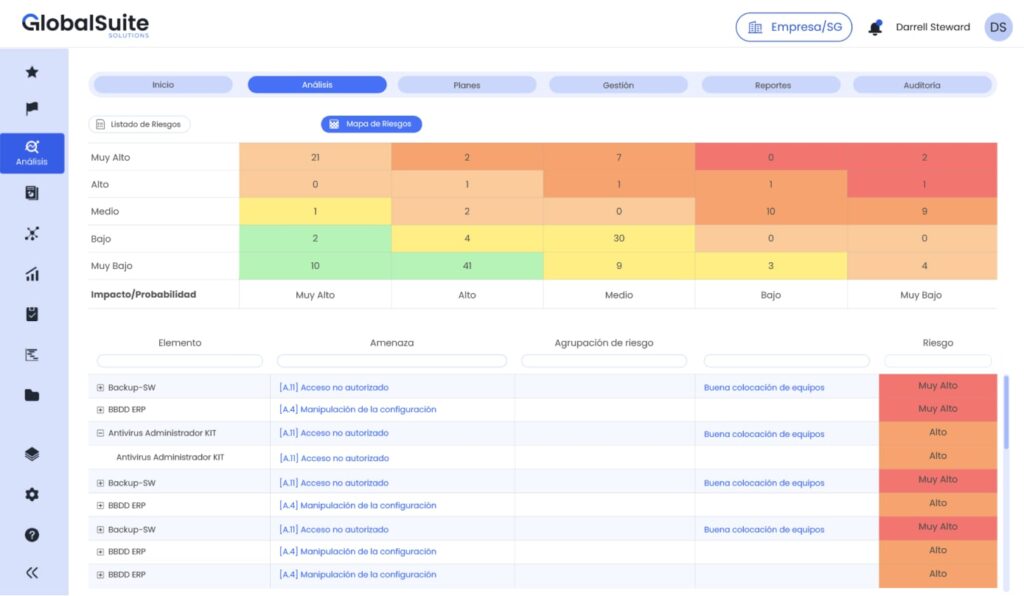
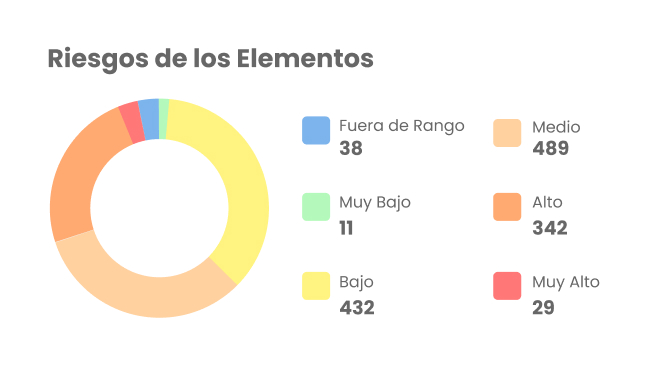
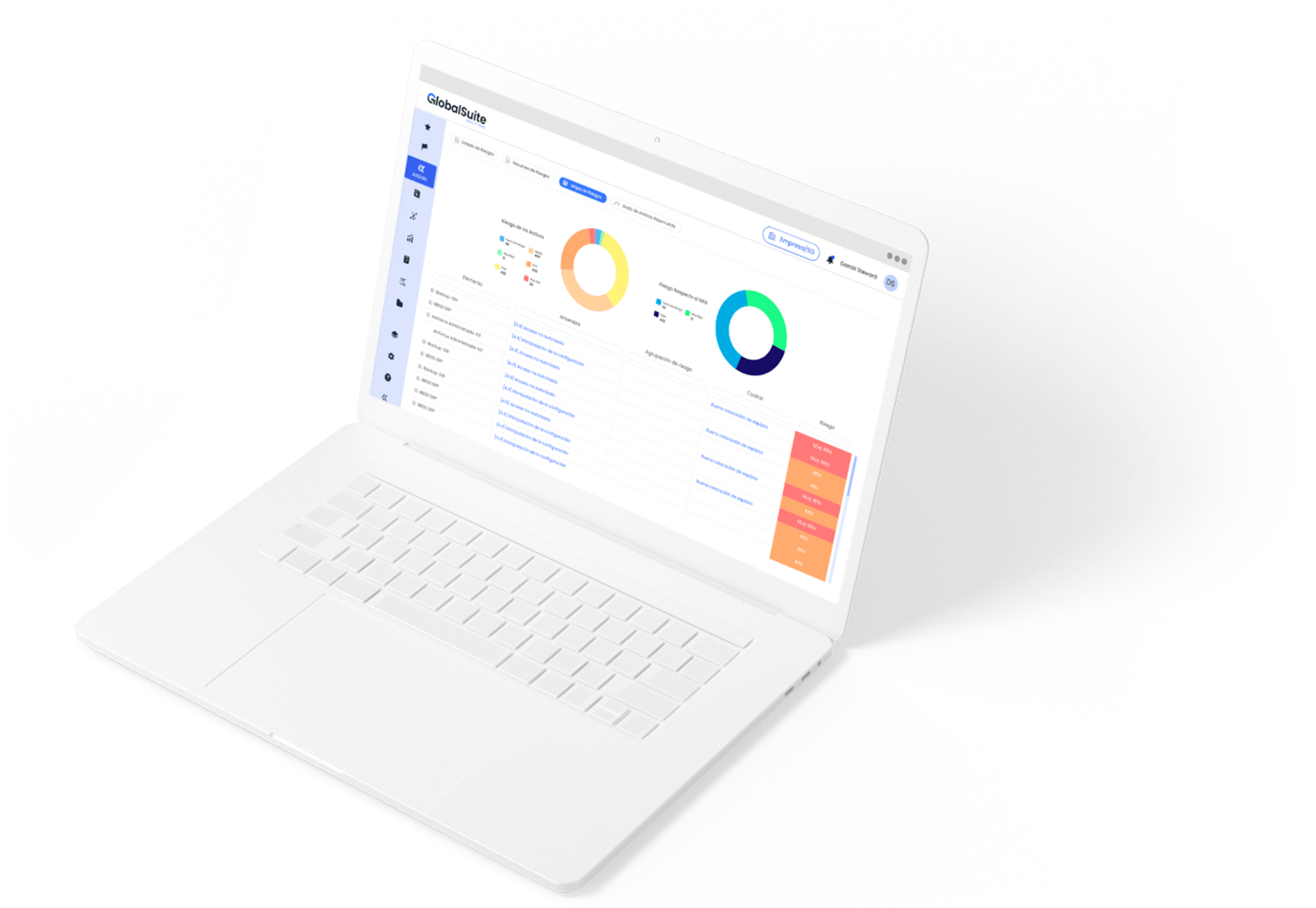
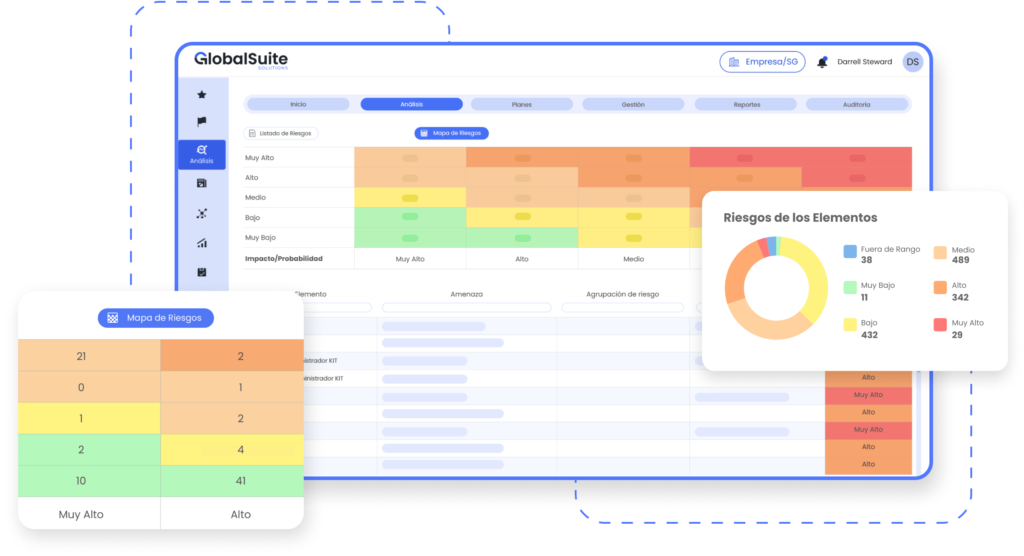
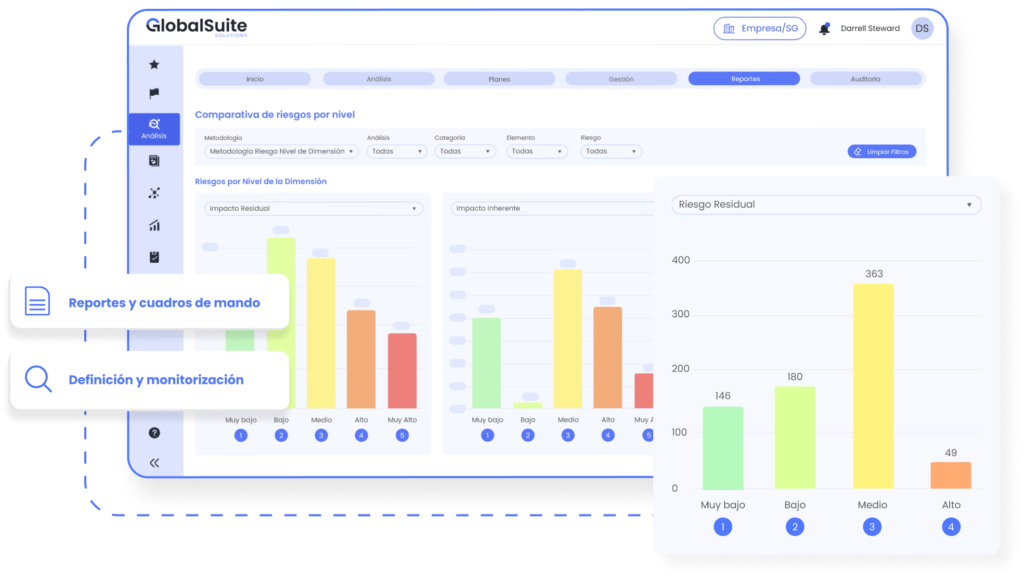
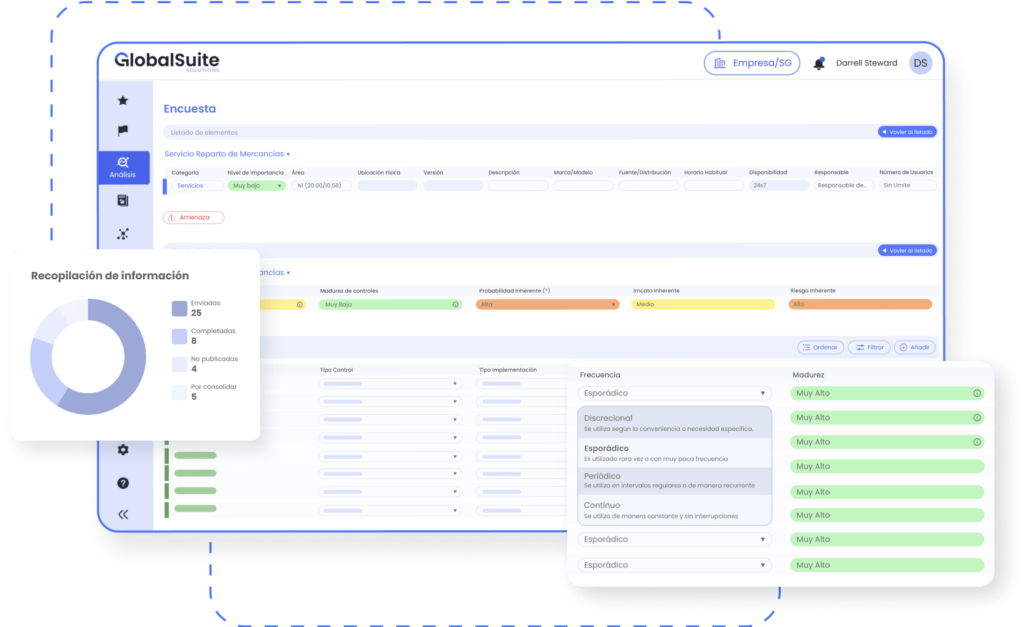
Transform your company’s information security management with GlobalSuite® Information Security, the end-to-end solution designed to automate and optimize ISO 27001 compliance. This specialized software makes it easy for you to implement, manage, and maintain Information Security Management Systems (ISMS), ensuring that you meet the most demanding standards in an affordable and intuitive way. With GlobalSuite®, you not only simplify the complexity of the ISMS, but also improve the protection of your most valuable assets.