Due to the growing need to implement effective cybersecurity measures in organizations as a result of numerous existing security attacks, the introduction of ISO standards in companies is a reality. ISO standards are standards developed and published by the International Organization for Standardization (ISO). The main objective of these types of standards is to regularize specific processes in areas such as Information Security.
Among these ISO standards, the so-called ISO 27000 family is one of the most prominent. This is a series of standards that detail the guidelines and requirements for implementing an Information Security Management System (ISMS).
Within this family, the main and certifiable one is ISO 27001. This specific standard details and provides the requirements for the establishment, implementation, maintenance, and continuous improvement of an ISMS.
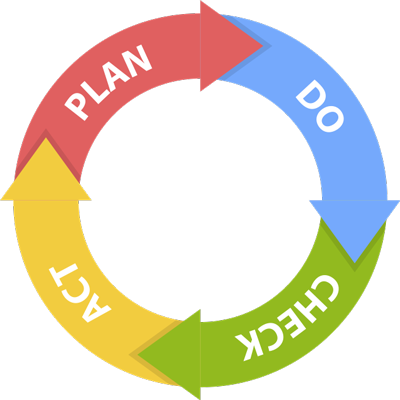
The Deming or PDCA Cycle in the ISO 27001 Standard
Delving into the content of the standard itself, the first part of it is composed of sections related to the topic discussed in this article. That is, with the well-known Deming or PDCA cycle. These sections are as follows:
- Context of the organization
- Leadership
- Planning
- Support
- Operation
- Performance evaluation
- Improvement
The PDCA cycle gets its name from the acronym: Plan-Do-Check-Act. Its methodology is based on continuous improvement, as a process can never be implemented with 100% effectiveness and precision. The words that give this cycle its name comprise the 4 phases that are distinguished in it.
Plan
The main objective of this phase is to establish the Information Security Management System. Specifically, in this step, the objectives, procedures, and policies related to Information Security will be established, with the aim of improving the latter.
Likewise, aspects such as the scope of the Management System, the roles, and their functions and responsibilities in the project should also be defined.
There are 4 sections of the ISO 27001 standard that are part of this first planning phase:
- Context of the organization
- Leadership
- Planning
- Support
The context section serves to define the first aspects of the Management System such as the context itself, encompassing everything that surrounds and affects the organization, the interested parties, and the scope of the Management System to be implemented.
Regarding the leadership point, this section is related to top management showing leadership and commitment to the process of implementing and maintaining the Management System. For this, a security policy is defined that should be known and applied by all those involved, as well as their roles and responsibilities.
Planning, which is the name of the next section of the standard, consists mainly of defining the Information Security objectives that the organization will establish. These objectives must be consistent with the developed security policy, measurable, communicated, and updated, as the standard itself indicates.
Finally, everything related to support is also considered in this phase. Here, different tasks or points to consider are distinguished. On one hand, there is the determination of the resources that will be essential for the implementation of the Management System, and the commitment to ensure their availability. On the other hand, it seeks to ensure competence and awareness, carrying out different security training actions for this purpose. Likewise, procedures for correct communication in the company must be taken into account. To conclude this section, the organization must consider the management of system documentation.
Do
At this point, the established ISMS will be implemented. The procedures established in the previous phase will be carried out and the necessary controls and operations will be implemented in order to manage the organization’s information in a secure and effective manner.
Regarding the correspondence of this phase of the cycle with the ISO 27001 standard, it is section 8 called Operation that addresses this point. For this, as mentioned previously, the defined Management System will be put into operation and implemented.
Standing out in this section are the creation of the inventory of information assets of the company, the risk analysis to understand its status, and the risk management carried out through the different Risk Treatment Plans.
Check
In this phase, which corresponds to the letter “C” of the PDCA cycle, the effectiveness of the Information Security Management System planned and implemented in previous phases will be evaluated and reviewed. To do this, it will be checked that aspects such as the security policy, objectives, or different implemented procedures are being met.
It is worth noting that these evaluations and reviews should be carried out periodically in order to ensure the correct implementation and operation of the procedures and actions taken to establish and implement the ISMS.
This phase of the Deming cycle could be said to be equivalent to section 9 of the ISO 27001 standard, the section called Performance Evaluation. At this point in the standard, it will be determined what needs monitoring and measurement, as well as the necessary methods to ensure valid results. For the monitoring, measurement, analysis, and evaluation of the ISMS, the organization should rely on sufficiently mature data to obtain adequate values that serve as a reference.
For this, metrics and indicators will be established to measure the effectiveness of the ISMS. In addition, procedures will also be created to carry out the internal audit and management review that will be conducted before proceeding with the external certification audit.
Act
In this final phase of the cycle, the ISMS will be maintained and improved. That is, both corrective and preventive actions and plans will be carried out to improve the results obtained and thus implement and achieve continuous improvement of the Information Security Management System.
This last phase corresponds to point 10 called Improvement of the standard discussed in this article. In turn, this section is divided into two parts. On one hand, management of non-conformities detected in the system is carried out at this point, both through internal/external audits and through company employees who, in carrying out their functions, detect possible deficiencies or non-compliances.
On the other hand, a continuous improvement process must be carried out. That is, a continuous ISMS maintenance process, in which the aim will be to improve the effectiveness and efficiency of the ISMS implemented by the organization.
At GlobalSuite Solutions, we have a Consulting area that can help you implement an ISMS based on the ISO 27001 standard, with extensive experience in this type of project for more than 10 years in companies from all types of sectors and businesses.
We have the GlobalSuite® software that facilitates the automation and management of the ISO 27001 standard to optimize your ISMS. The versatility of the software means that it meets the most complex requirements in an affordable and intuitive way, helping to obtain ISO 27001 certification and therefore improving the company’s cybersecurity.



